When we talk about developing a career in the tech industry, we have a tendency to only focus on one side of the coin. The technical skills. This is very important to anyone wanting to enter the field.
In my opinion, soft skills are as important but it is rare that we talk about how to improve these necessary traits. This post attempts to offer some ways to do just that for three skills: Research. Writing. Speaking.
Research
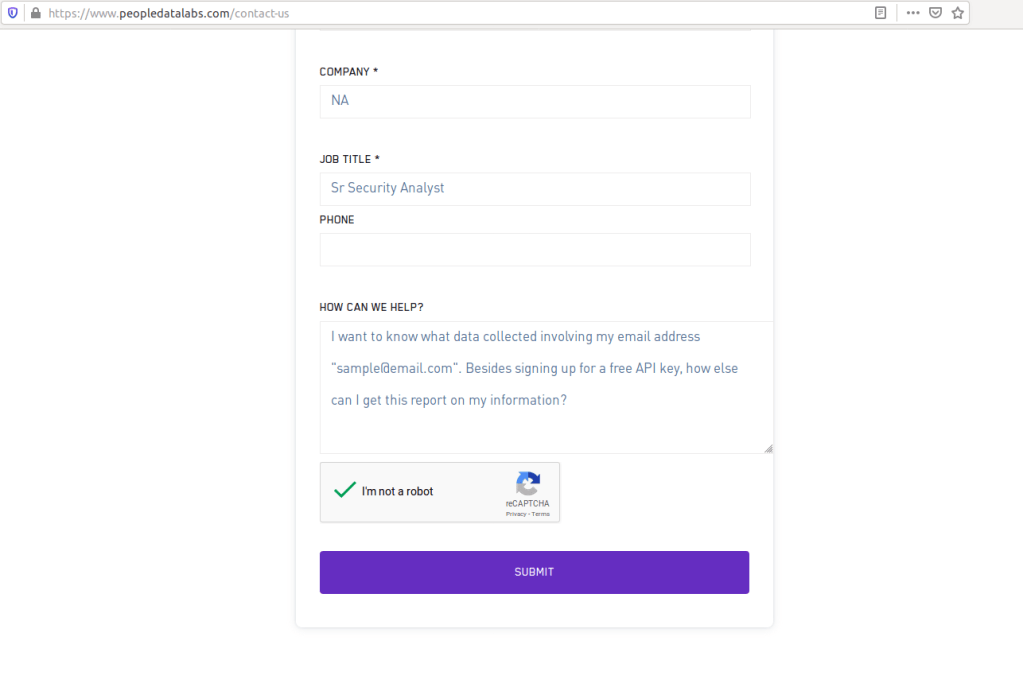
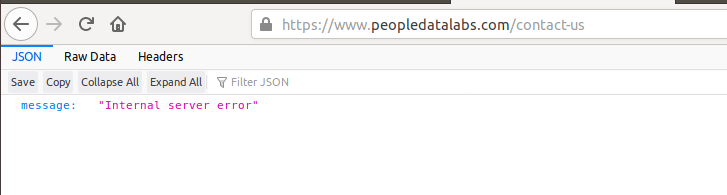
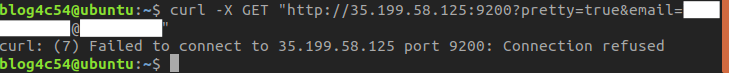
This is perhaps the most obvious soft skill that needs to be developed for anyone hoping to make a career in tech. Researching is more than hopping onto Google and finding a Stack Overflow article. It involves understanding what answer you are looking for.
Here are things to think about as you scour the internet for a solution.
- What are you trying to achieve?
- Making it work should not be good enough. Describe the behavior you want from the solution.
- What is the main roadblock to your solution?
- Understanding the problem is the best way to finding a solution. If you don’t know what the problem is, try looking it up or asking for another set of eyes.
- How old is the post/comment?
- You may find a solution to the problem you described but the post is from 2006. Systems and methods change over time. Are there any newer ones that fit your situation?
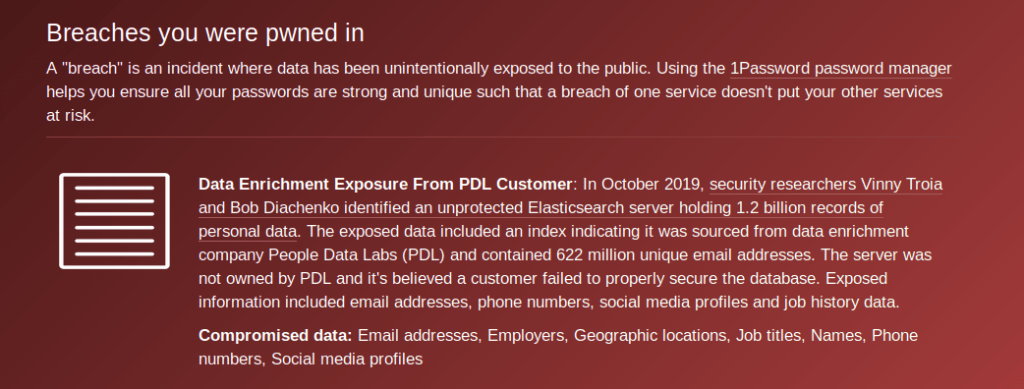
- Do I trust this site?
- Sometimes, Stack Overflow does not have the answers. Sometimes, the answer is on an unsecured blog webpage. You may have to take a chance on some sites but keep track of sites that have been reliable.
- What does my found solution do?
- Blind copy pasta can be dangerous. Especially if it is code related. Take some time to go over the solution to figure out what it does.
- Is this the only solution?
- Problems can have different ways of addressing it. Looking for variant solutions can help you choose the one that may be best.
Writing
Why should anyone develop their writing skills when they are in the matrix blasting malware?
Fair.
You don’t need writing skills while blasting malware. But what about afterwards when asked for a report on your findings? What if you are the only one with a foolproof method for resolving network issues? If there are problems while you’re out sick and someone else has to fix it, will they have documentation to work off of? Or will they have to call you? Worse yet, do you have to go in?
Effective writing reduces confusion and wasted time. This applies to code comments, investigation summaries, client emails, documentation, how-to guides and more. Keep these thoughts in mind when writing.
- What’s the goal?
- Is it to teach? Relay information? Get information? A memo?
- Who’s your audience?
- Is this only for yourself? Will colleagues/supervisors see it? Is this for your client? Who is your client and what do they do?
- How much detail is needed?
- Some people want a simple yes or no. Others may want to know exactly what was wrong and how it was fixed. Another group of people may want to know how a problem affects their goals.
- Will they understand you?
- Not everyone will know what a SIEM is or what port 80 is for. Try to avoid technical terms unless it is needed or there is no other way around it.
- Can this be repeated?
- This one is more for guides and how-to’s. Make sure the steps are as clear as possible for your audience. No point to writing a guide that no one can follow.
Speaking
This skill is deceptively hard. We all do it but we don’t always think about what we say or how it’s said. Besides communicating information, speaking can also garner trust from your audience.
Think about this.
You’re at a conference. A speaker gives a presentation on how quantum computing threatens modern-day encryption as we know it. Sounds interesting, right? But the speaker is constantly saying “umm” and does not sound like he knows what he is talking about. How would you feel?
Now, imagine being that speaker and seeing your audience take out their smartphone to play Pokemon Go.
Even if you are not giving presentations, it is important to take time to develop speaking skills. Doing so improves your chances during interviews, helps to build a good relationship with clientele, and prevents your audience from falling asleep.
Here are some things to think about before speaking.
- Are you sticking to the point?
- The point may take time to get to but don’t ramble…unless that’s what the audience wants.
- Who’s your audience?
- Same as with writing.
- What words to use?
- Is it safe to use technical words? If you’re giving a talk to accountants, do you know any of their words? Are some phrases better than others?
- Do you know what you’re talking about?
- How comfortable are you with the topic at hand? Do you rely on Powerpoint slides? Do you portray confidence?
- What’s your tone?
- Does the combination of words and tone sound like you’re blaming someone? If it is an emergency, does your speech convey urgency? Does your speech let the client know that they are in capable hands?
Conclusion
Developing these three skills takes time and does not always come easy. Myself included.
Fortunately, there are plenty of books, websites, and classes designed to develop these skills since they are found in just about every other industry in the world. So, if you want to take your career to the next level, definitely improve you soft skills and stay current in your field.