Another fun and relatively easy CTF from the website TryHackMe! I swear, this is by far my favorite site for learning pentesting techniques and getting some practical experience!
This CTF is about Pokemon and though you can probably guess the answer to “Find the Grass-Type Pokemon”, you probably won’t know how to present that answer. Good fun!
Deploy the machine and let’s get started!
First things first. We need some information about the machine. Run a basic nmap command for any open ports we may be able to leverage.nmap -sS -sV <ip_address>

We got http and ssh open. Can’t do much with ssh so let’s take a look at the website. One thing I like to do before navigating to the site is having something like gobuster searching for directories. gobuster dir -u <ip/domain> -w <wordlist>
When you go to the webpage of the ip address, you’re greeted with an adorable Apache2 default welcome page. Sorry, no Pikachu here. But maybe gobuster found something?
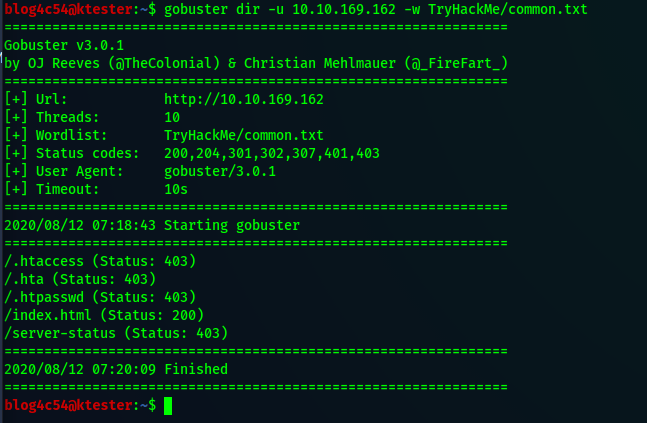
A bunch of 403s won’t do us any good. All we get is that default page…or do we?
At the very bottom of the webpage, there is something that looks out of place. A colon, all alone. To find out why it’s there, let’s look at the page source.
The source page has the typical css, javascript, and html trio. If you want, you can take some time with the javascript but it is not a clue. Believe me, I’ve tried. Instead look towards the bottom and there are two tags that doesn’t look like html.
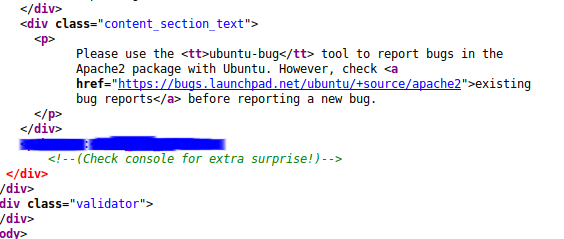
I’ll admit this took me a while to get and I face palmed myself once I realized what I was looking at. Right there in plain sight, ssh credentials! Now that we have those, we can leave the browser and ssh into the machine.ssh <user>@<ip_address>
Once we’re in, run the groups command. Our user is a part of many groups but not sudo. If we try sudo -l, we get a message that the user may not run sudo as root. Taking a look at the file permissions of /etc/passwd and /etc/shadow does not give us any kind of leverage we can use. And there’s nothing special in /etc/crontab. Looks like we won’t be escalating privileges yet so we’ll explore a little.
Running ls and ls -a on the home directory of our user does not yield anything interesting. If we look in the Desktop folder…

There is a zip file. Unzip it using the unzip command and we’ll see that our first flag is now available! There is a catch though. The flag is encoded. It is up to you figure out the encoding. Once you do, you’ll have the grass-type flag!
Going back to our home directory, we can list the contents of the other folders which gives nothing back except for one folder. The “Videos” folder has a folder called “Gotta”. Interesting. Navigate to that folder and the sub-folders that follow. There is a file at the end of the folder path that ends in “.cplusplus”. Run cat on this file.

We got credentials for another user! Before we use these credentials, let’s see if we can find any other flags as the user we currently are.
At this point, we still need the water and fire type flags. Good thing we can search based on keywords from the flags. We will use the find command to see if we can get the other two flags.find / -name "water-type*" 2>/dev/null
This shows us that there is a file called “water-type.txt” under /var/www/html. Run the cat command on the file and you’re presented with something resembling the flag. This flag needs to be decrypted and once again, I leave that up to the reader to figure out but as a hint, the ancient romans would be proud.
To find the fire-type flag, we will run the find command again but changing out the word “water” for “fire”.
find / -name "fire-type*" 2>/dev/null
Once again, we get a path to a file called “fire-type.txt”. Run cat on the file and you’ll get the third flag…encrypted. And as before, it’s up to you to figure out what the encryption is. All I can say is all your blank are belong to us.
What about root’s favorite pokemon?
Personally, I think it’s Psyduck but we got another set of credentials we can try out. Login to the other user’s account with the following command.su <new_username>
After logging in, run the groups command. You’ll see that this user is a part of sudo!
One thing you may notice quickly is that this user doesn’t have a home folder to go to. Check out the “/home/” folder with sudo ls -l.
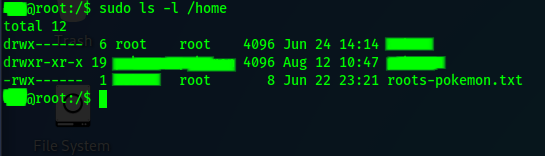
Although it’s redacted, we can see that our new user’s home directory is owned by root however we can read the “roots-pokemon.txt” file. Read it with the cat command to get the final flag! No tricks!
And that’s it! Congratulations on completing the CTF!
Side Note
When I originally did this challenge, I did not use the above steps after the initial ssh login. Instead, I was able to cat the .bash_history of the user and saw all of the commands taken to create the files for the flag and the additional user. I copied that to a temporary file in /tmp and used it as my guide to hunt the flags.
While writing this writeup, I found out that the .bash_history is now completely empty. This was certainly a surprise as I had thought that was the way to do the challenge. I now like to think I hacked the hacking challenge…or got really lucky that the bash history wasn’t cleared out.
Thank the hacking gods that there is a find command.